Credit Card Fraud increases:
In 2014, credit card fraud had an increase of 49% by data breaches over the previous year creating over 1 billion compromised data records.1 The 2015 report on credit card fraud was even worse with a 53% increase over 2014.2 Credit Card companies announced in 2012 that they would rollout a migration to replace current swipe only cards to EMV chipped credit cards by October of 2015. The fraud liability of “swipe-only” claims would be the responsibilty of the retail merchant after the October deadline. This extra security does not account for online transaction or what is called “card-not-present” purchases.
Fraud protection methods:
Current methods of online fraud protection techniques include merchants manually checking transactions for inconsistent items ordered, odd shipping locations and mismatched billing addresses. This can be time consuming due to the fact that less than 0.9% of online transactions are fraudulent.3 Another method would include using software tools such as Signifyd6 or Kount7 which can save a merchant time and money with no interruption to the customer waiting for an order to be fulfilled.
Online retailers should be familiar with tokenization in their current e-commerce stores or before investing in a new online payment method. Tokenization is the method of storing a customer’s credit card information on a third party system that is PCI compliant as opposed to storing it within the merchant’s servers.4 As no method is 100% secure, this method of not storing the customer’s credit card information on the merchant’s server nearly eliminates the risk of internal credit card theft or an outside hacker gaining access to the saved information.
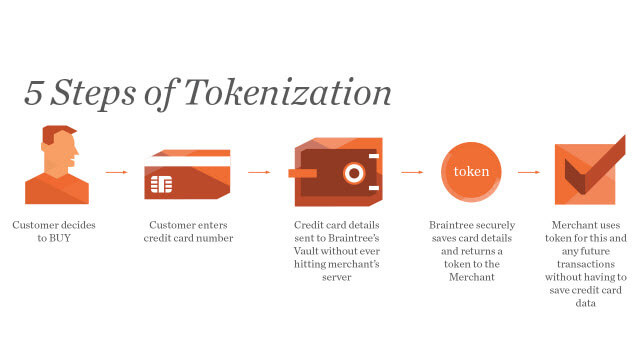
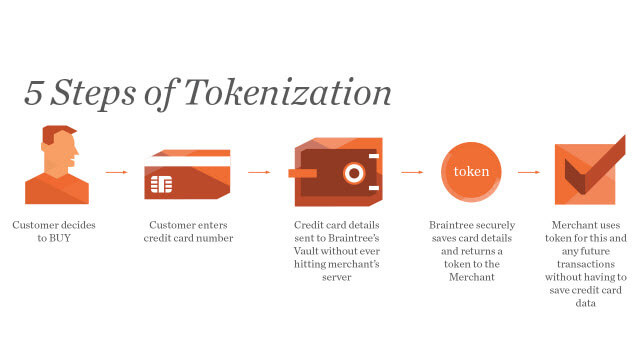
Here is how it works:
- A customer decides to purchase an item from the retailer’s site.
- A customer enters in their credit card number during checkout.
- The credit card information is not stored on the merchant’s server, but is passed directly to a PCI compliant merchant account gateway. Examples would include Braintree and Authorize.net.
- The PCI compliant merchant gateway will handle the transaction with the merchant account and then provide the online merchant with a token.
- The merchant will use this token to finish processing the transaction and any future transactions. The merchant never has a saved credit card on their servers and does not themselves need a PCI compliance certification.5
Problems with encryption:
A token is different from encryption in the fact that encryption uses a key to encrypt and decrypt the actual credit card information. If the encryption key is not managed properly the merchant will have issues with PCI compliance or even worse have it fall in the hands of a hacker.4
The key points to Tokenization:
- Using tokenization, the token is coded to be bound to a specific merchant gateway or third party PCS compliant party.
- A stolen token does not have the credit card information in it so a hacker in unable to use the token on another merchant or gateway.
- A merchant does not have to be PCI certified since credit cards are not being stored by the merchant.4
Sources:
- Gemalto’s 2014 Breach Level Index: http://www.gemalto.com/press/Pages/Gemalto-Releases-Findings-of-2014-Breach-Level-Index.aspx
- Gemalto’s 2015 Breach Level Index: http://www.gemalto.com/press/Pages/Gemalto-Releases-Findings-of-2015-Breach-Level-Index.aspx
- The Secret to Fraud Protection: https://magento.com/blog/best-practices/secret-fraud-protection
- Tokenization 101 with CIM and CRE Secure: https://community.developer.authorize.net/t5/The-Authorize-Net-Developer-Blog/Tokenization-101-with-CIM-and-CRE-Secure/ba-p/22911
- Why Tokenization is changing the way businesses do ecommerce: https://magento.com/blog/best-practices/why-tokenization-changing-way-businesses-do-ecommerce
- Top 4 reaons to use Signifyd: https://www.magentocommerce.com/magento-connect/fraud-and-chargeback-detection-prevent-fraud.html
- Kount Fraud Prevention Solutions: https://www.magentocommerce.com/magento-connect/kount-fraud-prevention-solution.html